Security experts have issued a stark warning after an Iran-linked attack on a major US company this week, cautioning it may only be the beginning.
The alert follows a cyberattack on Michigan-based medical technology giant Stryker that knocked thousands of employees offline and disrupted internal systems across the company's global network.
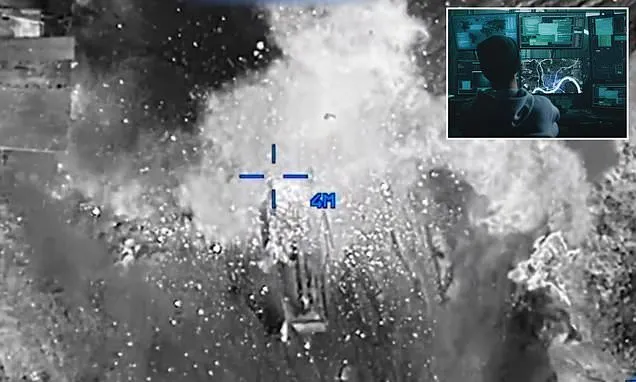
The Iran-linked hacker group Handala later claimed responsibility, describing the operation as retaliation for what it claimed was a US strike on a school in Minab.
Lee Sult, chief investigator at cybersecurity firm Binalyze, said the incident could mark the start of a broader campaign targeting Western organizations.
'The Stryker attack looks to be the first drop of blood in the water as a result of nation-state and hacktivist activity off the back of the Iran conflict,' he said.
'This attack confirms Western organizations are not only in the adversary's crosshairs, but the adversary can also make the shot. More shots are coming.'
Frank A Rose, former US Assistant Secretary of State for Arms Control and a policy adviser at the Defense Department, told the Daily Mail the incidents may signal a dangerous shift toward targeting American infrastructure.
Rose warned that data centers, banking systems, energy facilities, and privately owned infrastructure could be next on the Iranian hackers' list.
'When the Iranians know very well they cannot take us on head-to-head in America militarily, they're going to look for asymmetric ways to respond,' Rose said.
'Attacking American infrastructure might be one of those asymmetric vulnerabilities.'
He added that most of the US is commercially owned or privately held, and these groups do not think about security the way national security organizations do.
'You would hope companies in the private sector understand the evolving threat and start hardening key systems like data centers, banking networks and their cyber infrastructure,' said Rose.
'But that costs money. When I worked on cyber issues in government, we often didn't make the investments we needed to because there were always other budget priorities.'
'Since 9/11, we've improved security around critical infrastructure, but it's still not 100 percent.'
Sult said that the Wednesday cyberattack on Stryker 'be the first in a wave of attacks.'
The Handala group stated Telegram, saying it wiped more than 200,000 systems and extracted 50 terabytes of data in retaliation for military strikes on Iran.
The alert follows a cyberattack on Michigan-based medical technology giant Stryker that knocked thousands of employees offline and disrupted internal systems across the company's global network
Handala emerged around 2022 and has claimed responsibility for several cyberattacks against Israeli and Western targets.
The group claimed it shut down Stryker offices in 79 countries and that all extracted data is 'now in the hands of the free people of the world.' Stryker is active in over 100 countries around the world.
'Our major cyber operation has been executed with complete success,' Handala says in a statement, describing the attack as retaliation for what it calls 'the brutal attack on the Minab school' and for 'ongoing cyber assaults against the infrastructure of the Axis of Resistance.'
Children between the ages of seven and 12, along with staff members, were among those who died in the school strike. There were at least 175 people present during the February attack.
The company's staff found that remote devices running Microsoft's Windows operating system, such as cellphones, laptops and others configured to connect to Stryker's technology systems, had been wiped.
The logo of Handala appeared on login screens, according to the WSJ, which cited people familiar with the matter as well as social media posts.
However, Iran-linked hackers also launched a cyber campaign targeting US companies last week.
Cybersecurity experts revealed Thursday that the Advanced Persistent Threat (APT) group Seedworm had infiltrated multiple organizations, including a bank, an airport and a software supplier to the defense and aerospace industries.
Researchers at Symantec and Carbon Black discovered attackers installed a hidden malicious program, known as a backdoor, allowing them to secretly regain access to compromised systems.
Investigators said the hackers appeared to be spying, stealing sensitive data and positioning themselves for potential future attacks.
'These attacks are about sending a message rather than stealing information, which means any organization in the targeted country could be in the firing line,' the researchers warned.
The cyber activity comes as the US and Israel launched a major military offensive against Iran that killed the country's supreme leader and several senior officials.
'Because of the heated tension in the region and ongoing attacks, it is likely Iran and its allies may also initiate cyber operations to further target their adversaries,' the researchers said.